After making several different versions of Midbar, improving the encryption algorithm, improving the way it handles the PS/2 keyboard, and just making it more user-friendly, I realized that even with all these improvements, one thing is still missing - the ability to back up your data without literally hacking the device.
And so, I've decided to fix that "inconvenience" in the Midbar V5.0 by making it store user data on an SD card.
In case you want to know why I called this project Midbar - Midbar (מדבר) is a Hebrew word that means "pasture, " "uninhabited land, " "wilderness, " "large tracts of wilderness (around cities), " "desert." I had two reasons for choosing the word Midbar as the name of this project. First - while working on my previous projects, I noticed that the so-called "device that keeps your personal data secure in an encrypted form" market is pretty much a "desert around the oasis of the password manager market." Second - I couldn't find a better word to describe that project. At first, I wanted to call it a "Password Vault, " but then I realized it's more than just a password vault. So, I just called it Midbar!
You can also read this tutorial on Instructables and Medium.
3DES + AES + Blowfish + Serpent in CBC ModeThe "3DES + AES + Blowfish + Serpent" encryption algorithm in cipher block chaining mode first appeared in the Midbar V2.5. And since then has been utilized by the Midbar (Raspberry Pi Pico Version),Midbar V3.0,Midbar V4.0,KhadashPay V2.0,Midbar (Raspberry Pi Pico Version) V2.0, and KhadashPay V2.0 (Raspberry Pi Pico Version).
Although the "3DES + AES + Blowfish + Serpent" encryption algorithm ain't exactly what I would call "a cryptographically weak encryption algorithm, " operating it in a weird derivation of the ECB mode, the way it was done by the Midbar V2.0 wasn't the best idea that I had. Even though that wouldn't've allowed the attacker to produce the legitimate ciphertext by swapping the blocks within the ciphertext, an attacker could still make a legitimate ciphertext by replacing the nth block of the ciphertext N1 with the nth block of the ciphertext N2. To fix that vulnerability (instead of just notifying the user that the decrypted ciphertext might've been forged), I made the "3DES + AES + Blowfish + Serpent" encryption algorithm work in CBC mode. So, if an attacker replaces a block of ciphertext, it spoils not just that block but also the subsequent one.
I'll be honest with you, the bit-flipping attack "kinda works, " but I doubt that it would ever go unnoticed because of the "HMAC-SHA256"-based integrity verification feature.
And let's not forget that this encryption algorithm performs the operation called superencryption.
As defined by NIST, superencryption is an encryption operation for which the plaintext input to be transformed is the ciphertext output of a previous encryption operation.
Such organization of the encryption algorithms makes a combined encryption algorithm that is at least as strong as the strongest one in the cascade, has a longer key, might be more resistant to some attacks, and might produce a ciphertext with higher entropy. Anyway. It won't hurt to have an additional layer of security (or several of them).
And by the way, out of all encryption algorithms utilized by the Midbar V5.0, the "3DES + AES + Blowfish + Serpent" is the only algorithm that works in CBC mode. Beware of it!
Integrity VerificationThe Midbar V5.0 is the seventh version of Midbar that verifies the integrity of the whole record. So, the legitimate ciphertexts moved between the cells aren't much of a threat to it.
The "HMAC-SHA256"-based integrity verification feature works as follows:
When you add a record to Midbar, it concatenates all the data you've entered into a single string, computes a tag for it, and then stores that tag in the encrypted form.
When Midbar decrypts your data, it also decrypts the previously calculated tag and computes a new tag for the decrypted data. It then compares both tags, and if they don't match - Midbar notifies you that the integrity verification failed.
Configure Arduino IDE *OptionalIf you’ve never flashed ESP32 before — you’ll need to configure Arduino IDE and install drivers to upload the firmware to the boards. You can find the CP210x driver for ESP32 here: https://www.silabs.com/developers/usb-to-uart-brid...
In case you don’t have Arduino IDE, you can download it here: https://www.arduino.cc/en/software
Configuring IDE isn’t a part of this tutorial — you can read about it here: https://randomnerdtutorials.com/installing-the-esp32-board-in-arduino-ide-windows-instructions/
Download FirmwareYou can download the firmware for Midbar from one of these sources.
SourceForge: https://sourceforge.net/projects/midbar/
OSDN: https://osdn.net/projects/midbar/
GitHub: https://github.com/Northstrix/Midbar
If you just need the firmware for the device alongside the RNG, then I would advise you to download a 1.54 MB archive either from SourceForge, OSDN, or the code section down below.
But if you need the firmware for all versions of Midbar alongside the extra code, photos, and diagrams, in that case, I would advise you to download the 146 MB archive from GitHub.
Download and Install the LibrariesTFT_eSPI: https://github.com/Bodmer/TFT_eSPI
PS2KeyAdvanced: https://github.com/techpaul/PS2KeyAdvanced
PS2KeyMap: https://github.com/techpaul/PS2KeyMap
EncButton: https://github.com/GyverLibs/EncButton
Adafruit-GFX-Library: https://github.com/adafruit/Adafruit-GFX-Library
Adafruit_BusIO: https://github.com/adafruit/Adafruit_BusIO
Adafruit-ST7735-Library: https://github.com/adafruit/Adafruit-ST7735-Library
Keypad: https://github.com/Chris--A/Keypad
The process of unpacking libraries is typical. You can unpack the content of the archive into the folder:...\Arduino\libraries. Or open the Arduino IDE, click to the Sketch -> Include Library -> Add.ZIP Library... and select every archive with libraries.
Other required libraries are already present in one way or another.
Replace the Preset File for the TFT_eSPI LibraryTFT_eSPI Library requires the config to be adjusted depending on the display and the board that drives that display. Initially, I wanted to write the mini-guide on adjusting the config for the ILI9341 display to be properly used on the ESP32's HSPI. But then I realized that it would be more convenient to attach the adjusted config to the firmware and tell you where to place it.
Take the "User_Setup.h" file from the "ESP32_Version\V5.0" folder and place it in the "C:\Program Files (x86)\Arduino\libraries\TFT_eSPI-master" folder.
Switch the Partition Scheme to the "Huge APP (3MB No OTA/1MB SPIFFS)"You have to switch the partition scheme to the "Huge APP (3MB No OTA/1MB SPIFFS)" before you continue working with ESP32 because the firmware for the vault is too big for the default partition.
Generate KeysTo make the unauthorized deciphering of your data computationally infeasible - It is crucial to generate your own keys and never reuse them
It's entirely up to you how to generate the keys. I can only offer you an option to do so.
I've modified one of my previous projects to work as a random number generator, the generated output seems "random enough" for me, but I haven't run any tests. So, I can't guarantee that it's random.
Use it at your own risk!
To generate the keys - launch gen.exe from the "ESP32_Version\V5.0\Untested RNG" folder and click the "Generate keys for Midbar V5.0" button. The background turns from dark gray to light gray when you press that button.
Get the Receiver's MAC AddressTo get the receiver's MAC address, upload this code into the receiver board.
#include <WiFi.h>
void setup(){
Serial.begin(115200);
Serial.println();
Serial.println(WiFi.macAddress());
}
void loop(){
}Then open the Serial Terminal, and reboot the board.
If done correctly, you should see the MAC address in the console.
The MAC address of this board is 94:E6:86:37:FF:D8
Modify the FirmwareOpen the "Firmware_for_vault.ino" and "Firmware_for_receiver.ino" files, and then replace my keys with those you've generated.
Note that the receiver only needs three keys (hmackey_for_session_key, projection_key, proj_serp_key).
Don't forget to replace the receiver's MAC address in the line
uint8_t broadcastAddress[] = {0x94, 0xE6, 0x86, 0x37, 0xFF, 0xD8}; // Receiver's MAC address
in the "Firmware_for_vault.ino" file.
Flash the VaultUpload the firmware from the "ESP32_Version\V5.0\Firmware_for_vault" folder into the vault board.
Flash the ReceiverUpload the firmware from the "ESP32_Version\V5.0\Firmware_for_receiver" folder into the receiver board.
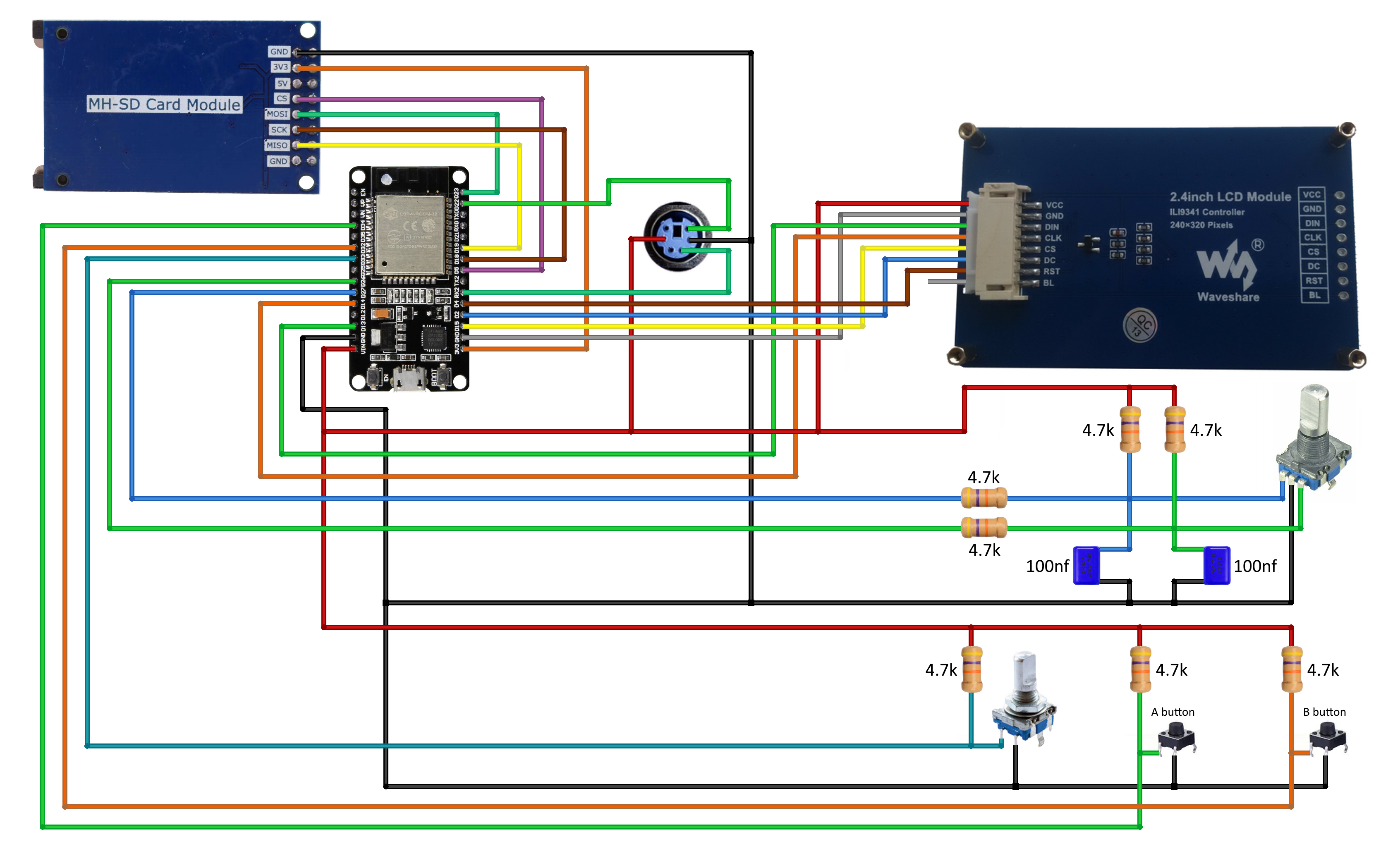
Assemble the VaultAssembling the vault shouldn't be hard. In my opinion, the most tangled part of the process is to connect the encoder with its periphery the right way.
As for the LCD's "BL" pin - I just left it hanging. But beware that some versions of the display might require you to connect it to the GND or to the 3.3V.
When it comes to the possible component replacements:
- You can replace 4.7k resistors with 4.7k - 10k resistors;
- And you can replace the capacitors with 22nf - 100nf capacitors.
Note that the SD card must have the FAT32 filesystem.
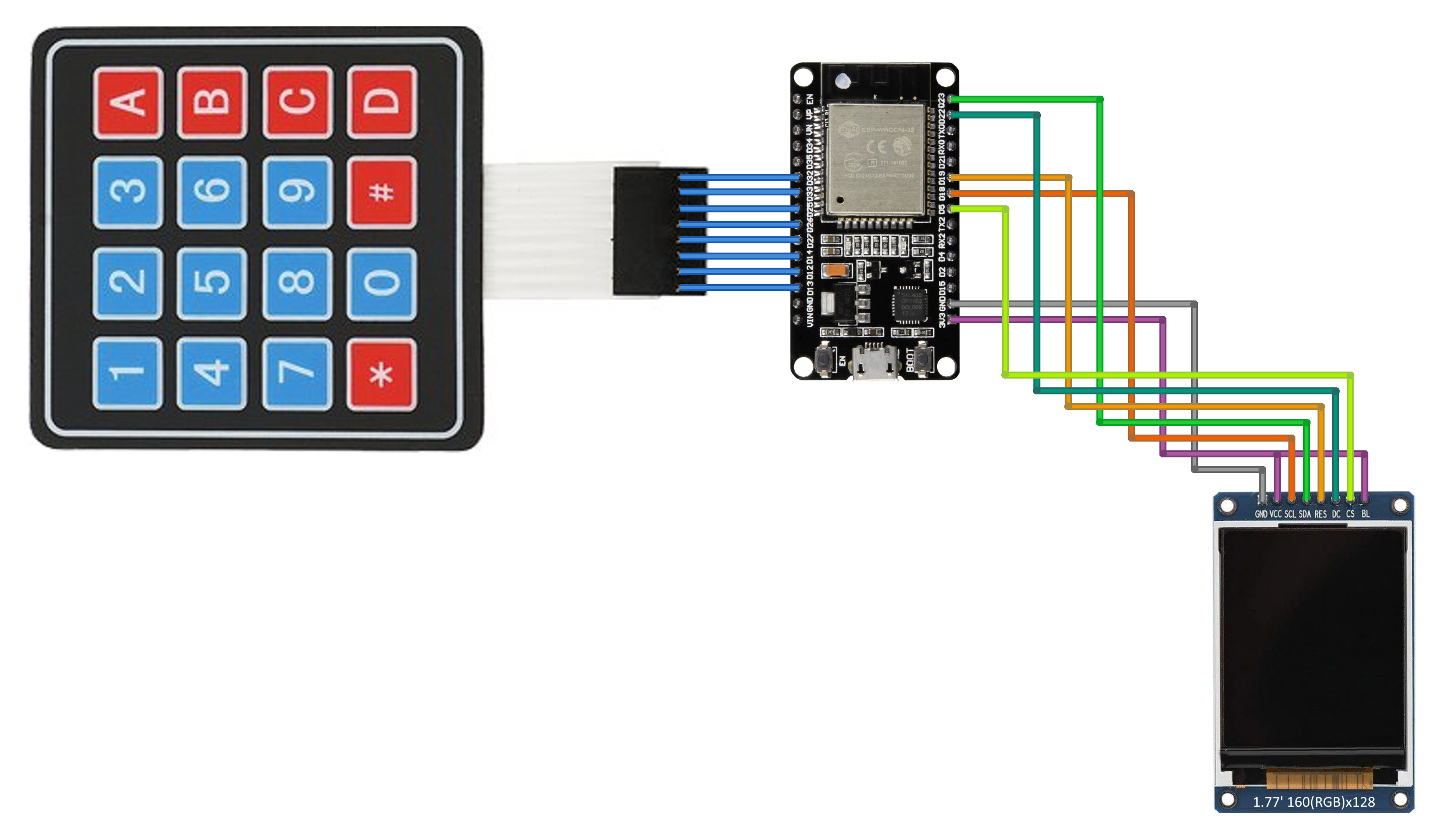
Assemble the ReceiverThat should be even easier than the vault assembly.
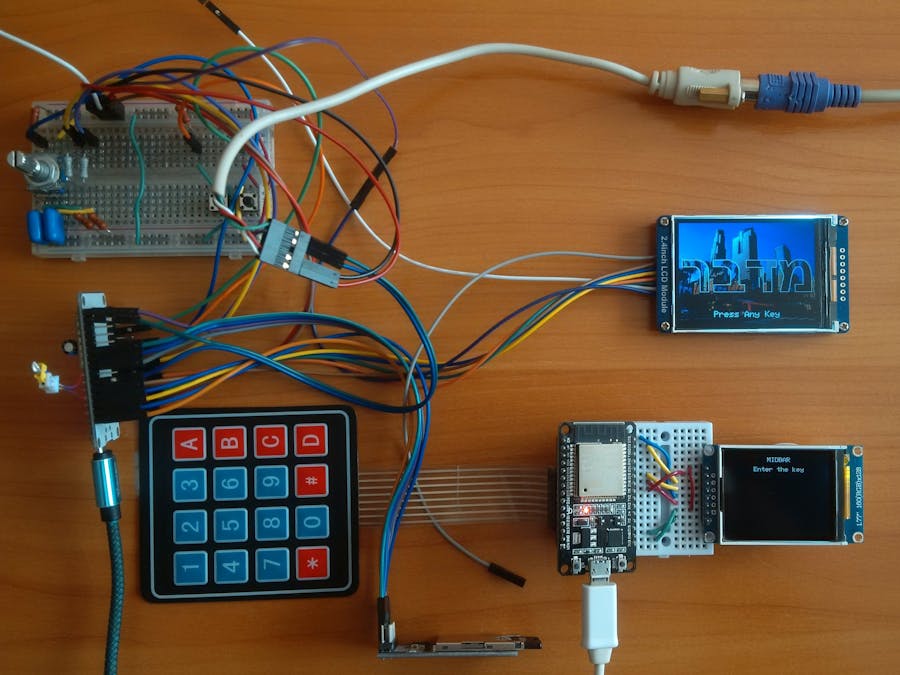
Power the Vault UpMidbar V5.0 has twelve lock screens. It randomly chooses one at a startup. After the Midbar has chosen the lock screen, it displays the word "מדבר" with the shifting background and the "Press Any Key" inscription.
*Credit for photos:
Photo by Piotr Chrobot on Unsplash
Photo by Erin Hervey on Unsplash
Photo by Jakob Rosen on Unsplash
Photo by Frank Chou on Unsplash
Photo by Ruben Christen on Unsplash
Photo by Olenka Kotyk on Unsplash
Image by JORGE TAPIA from Pixabay
Photo by Samuel Agbetunsin on Unsplash
Photo by Michael Beener on Unsplash
Photo by John Matychuk on Unsplash
Photo by Cristina Gottardi on Unsplash
Set the Master PasswordTo use the Midbar, you first need to set the master password.
You can only enter the master password using the encoder and PS/2 keyboard.
And remember that you can't change your master password without performing the factory reset first!
Midbar won't be able to decrypt your data without your master password because the keys for the encryption algorithms are partially derived from it. Perhaps, it won't even unlock without the correct master password.
When you're done entering your master password, either quad-click the encoder button or press the "Enter" on the PS/2 keyboard.
After you've unlocked the vault and got to the main menu:
- Either turn the rotary encoder to the right or press the "↓" (DOWNWARDS ARROW) key on the PS/2 keyboard to go down the menu.
- Either turn the rotary encoder to the left or press the "↑" (UPWARDS ARROW) key on the PS/2 keyboard to go up the menu.
- Press either the "A" button or the "Enter" key on the PS/2 keyboard to open the selected menu.
- While in the submenu, press either the "B" button or the "Esc" key on the PS/2 keyboard to return to the main menu.
While entering a text in a tab:
- Either quad-click the encoder button four or press "Enter" on the PS/2 keyboard to continue;
- Either quintuple-click the encoder button (click it five times in quick succession) or press the "Esc" button on the PS/2 keyboard to cancel the current operation.
*If the hex value decreases when you rotate the encoder to the right, I would advise you to swap the wires connected to the D26 and D27 pins.
And by the way, pressing the "Caps Lock, " "Num Lock, " or "Scroll Lock" buttons makes the keyboard unresponsive until you either reconnect it or reboot the ESP32.
Add LoginFirst and foremost, the Midbar V5.0 is a vault. It utilizes the 3DES + AES + Blowfish + Serpent encryption algorithm in CBC mode with an integrity verification feature alongside the SD card to keep your data safe and organized.
To add a login from the encoder and PS/2 keyboard:
- Select the "Logins" line in the main menu;
- Press either the "A" button or the "Enter" key on the PS/2 keyboard;
- Select the "Add" line;
- Press either the "A" button or the "Enter" key on the PS/2 keyboard;
- Choose the slot you want to put the login to either by rotating the encoder or by pressing the "←" (Leftwards Arrow) and "→" (Rightwards Arrow) keys on the PS/2 keyboard;
- Press either the "A" button or the "Enter" key on the PS/2 keyboard;
- Select the "Encoder + Keyboard" line;
- Press either the "A" button or the "Enter" key on the PS/2 keyboard;
- Enter the title;
- Either quad-click the encoder button or press "Enter" on the PS/2 keyboard;
- Enter the username;
- Either quad-click the encoder button or press "Enter" on the PS/2 keyboard;
- Enter the password;
- Either quad-click the encoder button or press "Enter" on the PS/2 keyboard;
- Enter the website;
- Either quad-click the encoder button or press "Enter" on the PS/2 keyboard.
According to the tests I've conducted - ESP32 can encrypt and decrypt a 650-character long string without any problems using the 3DES + AES + Blowfish + Serpent encryption algorithm. So, technically, you can put 650 characters into a field of a record.
*All credentials demonstrated here are entirely fictitious. Any similarity to actual credentials is purely coincidental.
View LoginTo view a login:
- Select the "Logins" line in the main menu;
- Press either the "A" button or the "Enter" key on the PS/2 keyboard;
- Select the "View" line;
- Press either the "A" button or the "Enter" key on the PS/2 keyboard;
- Choose the slot you want to view login from either by rotating the encoder or by pressing the "←" (Leftwards Arrow) and "→" (Rightwards Arrow) keys on the PS/2 keyboard;
- Press either the "A" button or the "Enter" key on the PS/2 keyboard;
- Press either the "Tab" key on the PS/2 keyboard or the encoder button to print the record to the serial terminal.
*All credentials demonstrated here are entirely fictitious. Any similarity to actual credentials is purely coincidental.
Edit LoginTo edit a login:
- Select the "Logins" line in the main menu;
- Press either the "A" button or the "Enter" key on the PS/2 keyboard;
- Select the "Edit" line;
- Press either the "A" button or the "Enter" key on the PS/2 keyboard;
- Select the login you would like to edit either by rotating the encoder or by pressing the "←" (Leftwards Arrow) and "→" (Rightwards Arrow) keys on the PS/2 keyboard;
- Press either the "A" button or the "Enter" key on the PS/2 keyboard;
- Select the input source;
- Press either the "A" button or the "Enter" key on the PS/2 keyboard;
- Depending on the chosen input source, either enter the new password you'd like to set on the encoder and PS/2 keyboard or paste it to the Serial Terminal;
- Depending on the chosen input source, either quad-click the encoder button (or press "Enter") or press the "Send" button in the Serial Terminal.
*All credentials demonstrated here are entirely fictitious. Any similarity to actual credentials is purely coincidental.
Delete LoginTo delete a login:
- Select the "Logins" line;
- Press either the "A" button or the "Enter" key on the PS/2 keyboard;
- Select the "Delete" line;
- Press either the "A" button or the "Enter" key on the PS/2 keyboard;
- Select the login you would like to delete either by rotating the encoder or by pressing the "←" (Leftwards Arrow) and "→" (Rightwards Arrow) keys on the PS/2 keyboard;
- Press either the "A" button or the "Enter" key on the PS/2 keyboard.
The process of working with records of other types is very similar to the process of working with logins.
Send Password to the ReceiverI made this feature to give you the ability to securely send a password to a distance of up to 650 feet (200 meters).
To protect the receiver from the replay attack (ensure that the receiver won't correctly decrypt any package that is resent to it) - I've combined the key incrementation with the session key. The session key consists of 20 characters generated by the vault. The session key is valid until you either reboot vault or power it off. After the key derivation process completes, both devices present you with the three verification numbers. These numbers must match on both the vault and the receiver! If these numbers don't match, I would advise you to reboot the receiver board and enter the session key again. If that won't work, open the firmware and check if the keys are the same.
To send the password to the receiver:
- Select the "Other Options" line in the main menu;
- Press either the "A" button or the "Enter" key on the PS/2 keyboard;
- Select the "Send Password" line;
- Press either the "A" button or the "Enter" key on the PS/2 keyboard;
- Enter the key on the receiver's keypad ('#' = 'E' '*' = 'F');
- Compare the verification numbers on both displays. They must be the same;
- Press either the "A" button or the "Enter" key on the PS/2 keyboard;
- Enter the password you'd like to send on the encoder and PS/2 keyboard;
- Either press the "Enter" key on the PS/2 keyboard or quad-click the encoder button to send the password to the receiver.
The receiver also prints the received text to the Serial Terminal.
According to the quick tests I've conducted, the Midbar V5.0 can transfer a 200-character long string over the air without any problems.
*As you might've noticed, I've reused some photos from the tutorial for the Midbar V3.0 and the tutorial for the Midbar V4.0 because the GUI is basically the same. The only thing that changed is the position of the inscription informing you about the integrity of the record. It used to be centered, but now it's aligned to the left.
Find a Good Use for MidbarFinally, there's a version of Midbar that allows you to back up your data without the need to hack it. Unfortunately, not all parts of Midbar are as good as that one - as for the features in the "Encryption Algorithms" submenu, you can encrypt and then decrypt a 30-character long string with the 3DES + AES + Blowfish + Serpent encryption algorithm in CBC mode with a properly working integrity verification feature, but that's basically as far as it can go.
If you need a version of Midbar where the features from the "Encryption Algorithms" submenu work as they should. I suggest you use Midbar (Raspberry Pi Pico Version) or Midbar (Raspberry Pi Pico Version) V2.0 - each of them can easily encrypt and then decrypt a 10 000 character-long string without any problems.
By the way, let me remind you that the Midbar project isn't there to give you a 100% guarantee for something. It's not about that, and it never was. It's about raising the cost of unauthorized access to your data as high as possible!
If you want to make your own version of the Midbar or change something in it, please do so! Don't forget that there's always room for improvement, even if it seems that there's none. Ok, that's it for this tutorial.
If you like this tutorial, please share it.
And if you have any Midbar-related questions, don't hesitate to ask them in the comment section.
Thank you for reading this tutorial.








Comments
Please log in or sign up to comment.